Our engineering team was just configuring some SonicWALL firewalls that we manage for clients and we came across a SonicWALL firewall vulnerability worth sharing.
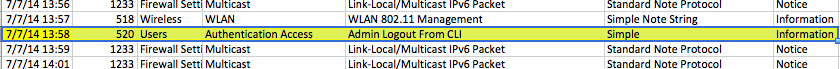
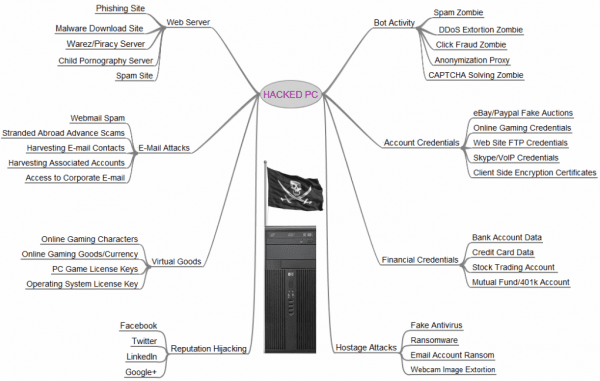
SonicWALL firewalls have the ability to be managed via command line interface (CLI) over SSH. Two of the primary benefits for an IT group to manage them like this are speed and security. We discovered today that enabling SSH even with a strong password on SonicWALL devices with 5.9 firmware versions, maybe even 5.8 versions, with almost 100% certainty allow your network to be hacked with some widely available tools, even if you have Geo-IP filters and an IP blacklist enabled. When SSH access is turned on in the firmware versions we tested, SSH firewall rules are automatically created to be open to all public IPs. If you have a SonicWALL firewall on your network and aren’t 100% certain that you have this vulnerability addressed, please look into it or send us an e-mail if you aren’t sure. We will be glad to help.
Solutions
Boost IT
3365 Piedmont Road NE
Suite 1400
Atlanta, GA 30305
(404) 865-1289
© 2026 Boost IT. All Rights Reserved.